BSidesSF 2019 CTF Writeup

CTF page: https://ctftime.org/event/753
Team: NoPwnNoGain
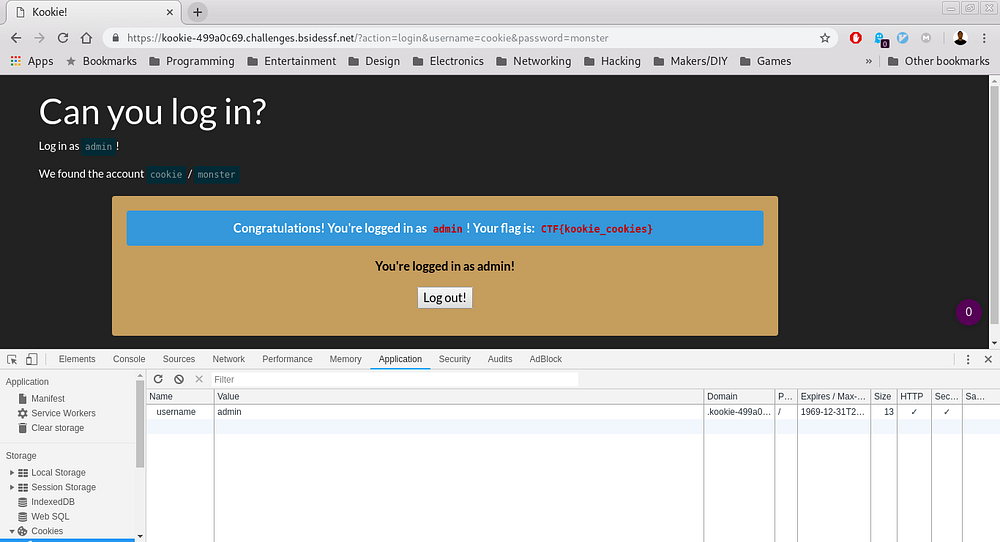
Zippy
Description
Can you read the flag from the PCAP?
We are provided with zippy.pcapng file.
Opening the file in wireshark and checking the stream, I see a zip file is being sent and the password of the zip as well.
I then sorted the packets with length to identify the largest as I assumed that will be our file. To get the file, select the packet then File → Export packet bytes → Save it as flag.zip
unzip -P supercomplexpassword flag.zipFlag: CTF{this_flag_is_your_flag}
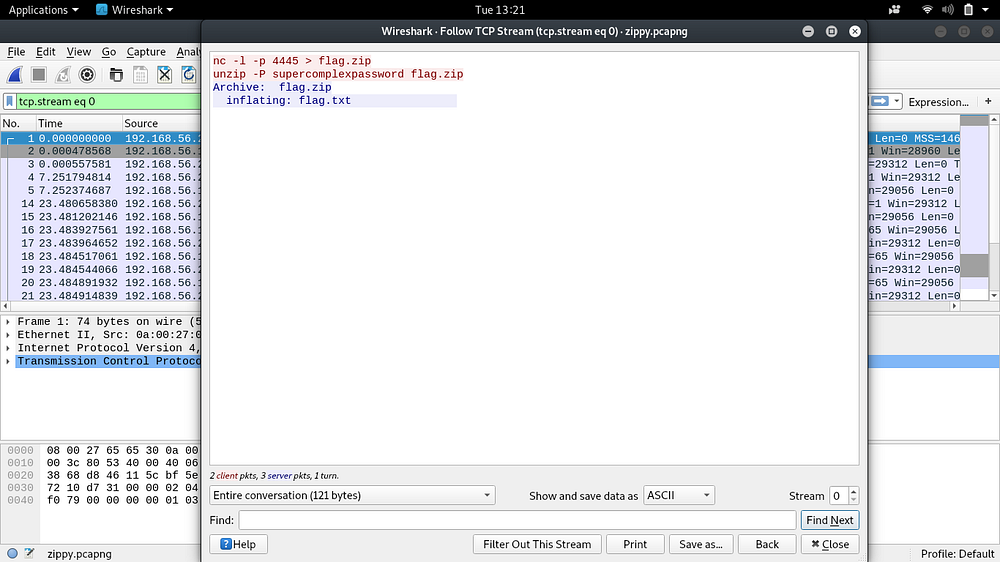
Table-tennis
Description
The flag is in the Pcap, can you find it?
We are given out.pcapng file. Inspecting the file in wireshark most of the traffic is encrypted TLS so nothing could be read. I then sorted the packets and found some ICMP packets that I had ignored had some data in them.
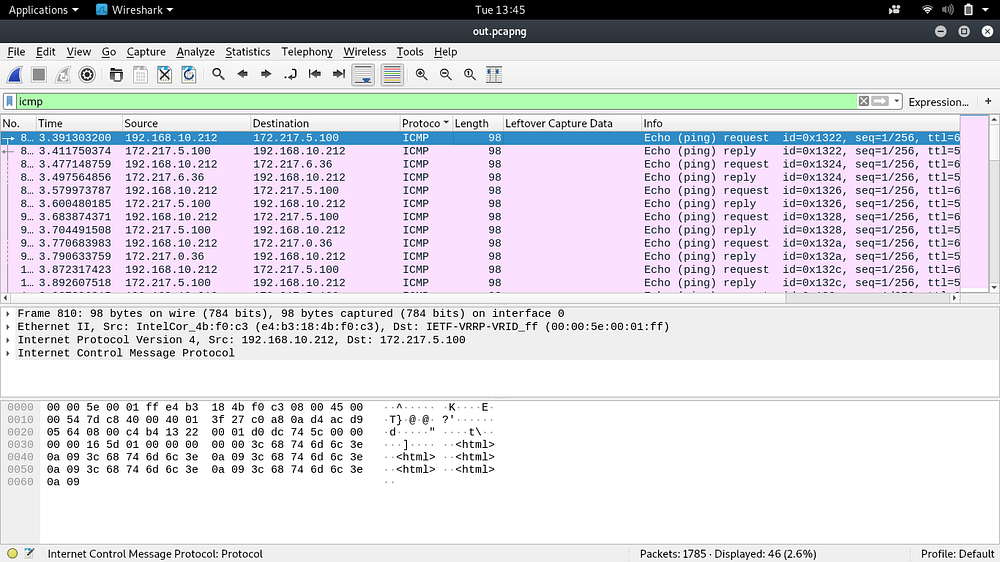
Instead of using wireshark to inspect each of them and get the information, I thought of using scapy to make it easier.
Here’s what the script recovered.
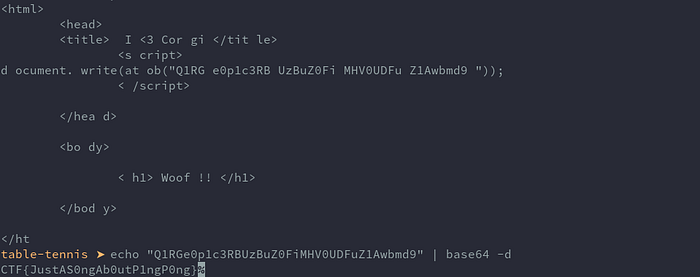
Decoding the string inside the <script> tags and removing the spaces I got the flag.
Blink
Description
Get past the Jedi mind trick to find the flag you are looking for.
We are provided with a blind.apk file. First used apktool to decompile it.
apktool d blink.apkGoing into the smali folder created by apktool
blink/smali/com/example/blinkThere’s a r2d2.smali file. Inside there’s a string of base64 encoded image.
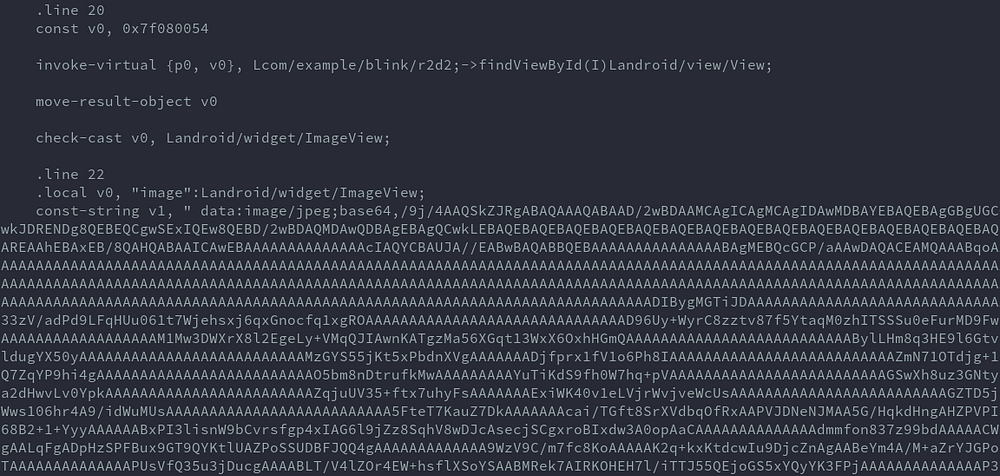
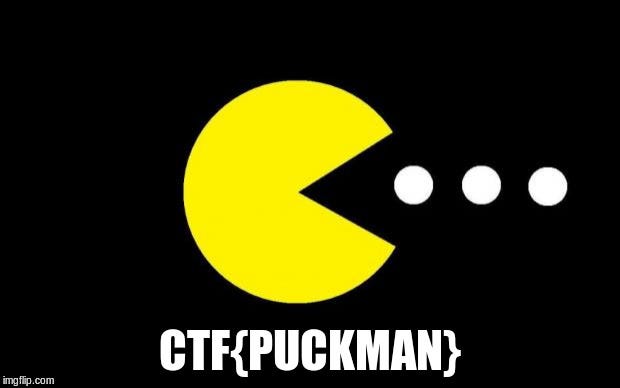
Decoded the image and got the flag.
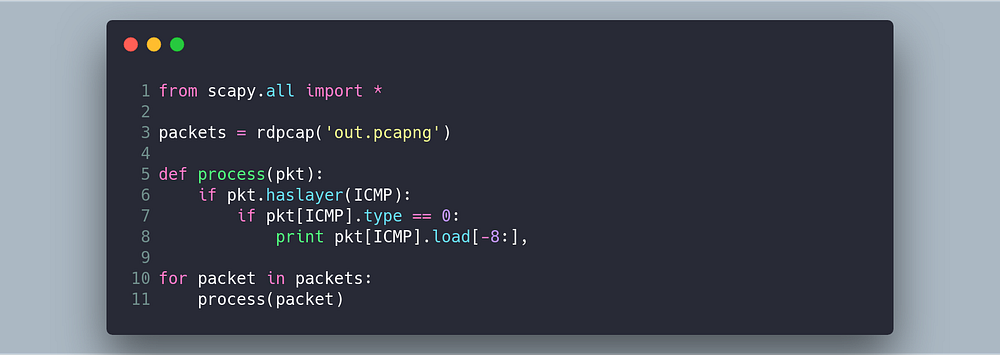
Kookie
All you had to do was change cookie to admin.
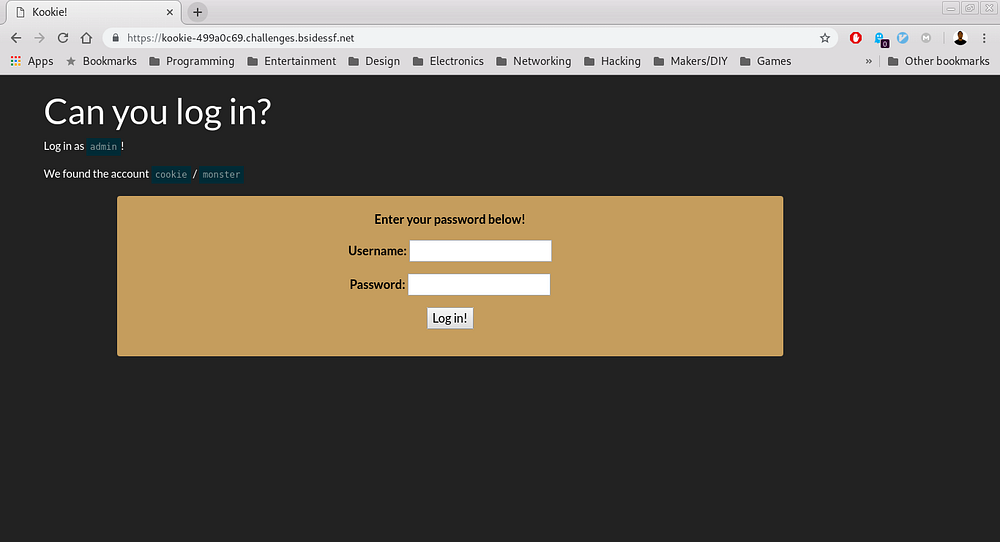
Flag: