Access — HTB Writeup
Intro
After solving a few VMs from Vulnhub I came across hackthebox. What intrigued me about the site was the first challenge you have to solve to register yourself. I knew then it wasn’t going to be like other platforms. At first it was it was intimidating as even setting up the vpn looked like a complicated task to me, so I didn’t use it for a while.
Few months later I decided to go back and actually tackle the machines and challenges, since then I have been on it constantly and I’ve learnt a lot in such a short time.
The hackthebox machines are set up in two objectives of getting a user on the machine where the flag is a user.txt in home directory and then post exploitation to get root user and read root.txt in root directory. For windows these files will in the Desktop folder.
This is my first hackthebox machine writeup! Let’s get into it.
Getting User
As always first step is detecting services that are running on the machine.
nmap -sC -sV -oN access-tcp.scan 10.10.10.98
We get three services running that reveal this is a windows machine. Going for the low hanging fruit first is to check ftp as it has anonymous login enabled.
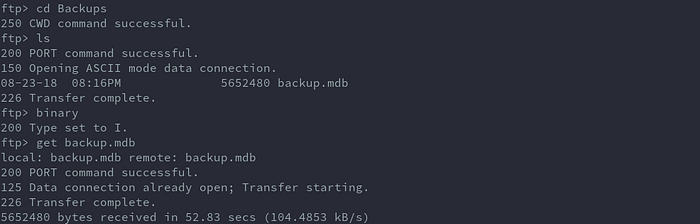
The login works and there are two folders (Backups and Engineer) present, let’s check if there are any files and the download them.
There’s one file in Backups, backups.mdb, and another in Engineer, Access Control.zip.

When downloading the backup.mdb, putting the mode in binary helps download the file properly. Check that the file sizes match after downloading.
Once downloaded, I find the zip file is password protected.

So let’s check the backup.mdb, which is a Microsoft Access Database.

Running strings to see if anything interesting comes up.
strings backup.mdb | lessScrolling through the output slowly I came across this:

Let’s try access4u@security as the password for the zip file, it works and extracts. We now have a new file, Access Control.pst, which is a Microsoft Outlook email folder.
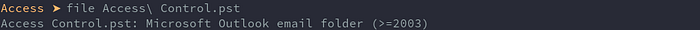
After a bit of googling I found there’s a tool called readpst to read .pst files. It creates an .mbox file which is easily readable. Reading the .mbox file created, this message is in the email message body. A mention of password being changed.
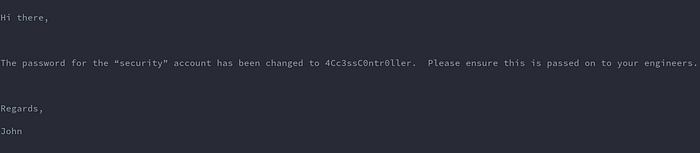
I used this credentials to login the telnet port we found open.
Account: security
Password: 4Cc3ssC0ntr0ller

Login works and we can read user.txt in Desktop folder.
Getting Root
Now for privilege escalation. Rooting this box was somewhat easy if you had a good idea of the command to run and it’s syntax.
Local enumeration, I wasn’t sure how to do this but someone in the forum hinted about checking for stored credentials. After some researching I found cmdkey command can list cached credentials in the Credential Manager Database. This cheatsheet has more stuff to check for when enumerating for privesc.
https://www.absolomb.com/2018-01-26-Windows-Privilege-Escalation-Guide/
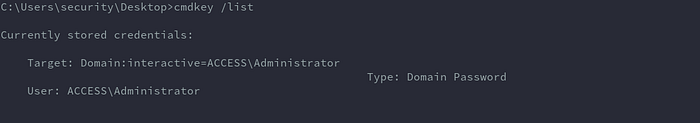
Now that we know there are stored creds how would we abuse this? Clueless me went back to the forum for hints and someone mentioned using runas command to run commands as another user.
After googling I found the right syntax to use so as to use the stored credentials but I had to test the command to be sure, using the telnet shell was very slow for testing.
runas /savecred /user:Administrator "c:\windows\system32\cmd.exe /c type \"C:\Users\Administrator\Desktop\root.txt\" > \"C:\Users\security\Desktop\roothash.txt\""What the command is doing is, it uses the /savecred option to use the stored credentials followed by the user we want to runas then runs cmd.exe and uses /c to give it the type command which outputs the contents of root.txt to roothash.txt in our user’s desktop directory. This means you can run any command as root user using this method but I just got root.txt for proof.
Note to properly escape the some of the quotes.

Running cmd this way is a bit blind because it opens a new cmd window, so we can’t see any errors that the command encounters. Trying it on a windows machine helps get the syntax right and see how it behaves.
Extras
The web server running on port 80 was a dead end, it just had a web page with an image of a server.
Some links I found that I think relate to the challenge and could be helpful.
http://theevilbit.blogspot.com/2013/01/backtrack-forensics-convert-pst-mail.html
Conclusion
This was a great box to refresh on cmd commands and also one way to privilege escalate a windows machine when an admin has saved their credentials. The provision of windows machines on hackthebox is what I think makes it a really great platform to practice on.
Will posting more writeups and stuff I learn, feedback is appreciated :).
hackthebox: ikuamike
Twitter: ikuamike
Github: ikuamike
